Hello world!
Welcome to WordPress. This is your first post. Edit or delete it, then start writing!

Protect What PowersYour Business
Mor Platform, a practitioner-led OT cybersecurity suite built by OT engineers to deliver deep asset visibility, actionable risk insight, and operational resilience—without disrupting industrial operations
The Mor Platform is delivered through four tightly integrated solutions, each addressing a critical dimension of OT cybersecurity while working together as a unified system:
Deep OT asset visibility and vulnerability intelligence
Unauthorized Change Detection for OT Systems
Intelligent OT Obsolescence Management
Backup, recovery readiness, and operational resilience
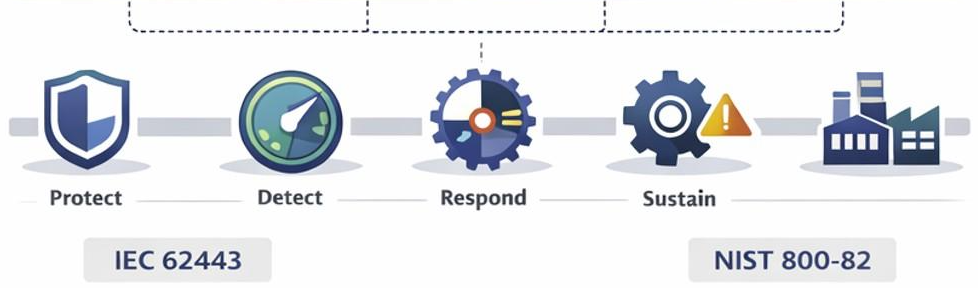
Each solution can be deployed independently or together, allowing organizations to adopt Mor at their own pace while building toward a comprehensive OT cybersecurity and resilience posture.
Mor Insights Integration with external systems – SIEM, SOAR or Cybersecurity Systems
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, […]
View CSAF Summary Successful exploitation of this vulnerability may enable an attacker to access […]
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based […]
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based […]
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in […]
View CSAF Summary Successful exploitation of this vulnerability could allow a standard user to […]
View CSAF Summary Hitachi Energy is aware of a vulnerability that affects the Hitachi Energy PCM600 […]
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in […]
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in […]
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on […]
CISA, in collaboration with the Australian Signals Directorate’s Australian Cyber Security Centre […]
View CSAF Summary This vulnerability was privately reported relating to ABB’s implementation of […]
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to send a […]
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to send […]
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to bypass […]
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to […]
View CSAF Summary ABB became aware of vulnerability in the products versions listed as affected in […]
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, […]
Adapting Zero Trust Principles to Operational Technology CISA, in coordination with the Department […]
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to disclose […]
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, […]
CISA has added four new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based […]
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to bypass […]
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on […]
Malware Analysis Report at a Glance Malware Name FIRESTARTER Original Publication April 23, […]
View CSAF Summary Successful exploitation of this vulnerability could result in an attacker being […]
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to […]
Defending against china-nexus covert networks of compromised devices executive summary Defending […]
View CSAF Summary Successful exploitation of these vulnerabilities could crash the device being […]
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to read, […]




Essway is a team of OT engineers, cybersecurity experts, and seasoned entrepreneurs focused on protecting the systems that power critical operations.
Our Mor platform delivers deep OT visibility, vulnerability and lifecycle insights, and change detection—built for zero interruption and real-world industrial constraints, including air-gapped environments.

Trusted OT security experts delivering cutting-edge solutions to defend
against sophisticated cyber threats. Proactive protection with deep visibility,
threat intelligence, and resilient OT security strategies.

Trusted OT security experts delivering cutting-edge solutions to defend
against sophisticated cyber threats. Proactive protection with deep visibility,
threat intelligence, and resilient OT security strategies.



Still unsure about our features? Request a demo today and see how our advanced OT security solutions can protect and enhance your critical infrastructure in real-time!
Welcome to WordPress. This is your first post. Edit or delete it, then start writing!
Copyright © 2026. All rights reserved